Cloud access
Available
T3-CAPa
Available
T3-CAPp (/ID:nnnn)
Default
VPN/IPsec
Required
SSH-2(2) (3)
Required
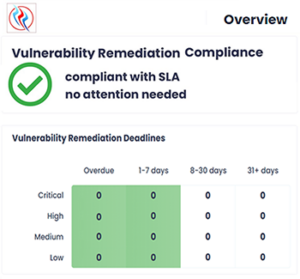
Compliance status
- The system doesn’t generate values blindly — it factors in recent server load.
- Endpoints and V-terminals reflect both current and anticipated demand.
- If you refresh quickly, the system hasn't stabilized — it’s still adjusting from previous snapshots.
- This creates more variation and shows a more dynamic, real-time snapshot.
Bottom line: The sooner you refresh, the more unique each snapshot becomes. You're seeing the system respond in real time — like taking rapid pulses.
(1) On-demand snapshot. For live VRC, SLA, and HIPAA compliance updates, as well as Client Terminal health status updates, please use the Client Portal.
(2) Security standards require key rotation at regular intervals. As part of our routine security protocols, we rotate SSH keys to enhance security and mitigate potential risks.
- On-Site Key Generation – The process of generating cryptographic keys never occurs remotely or off-premises, ensuring physical security and control over sensitive information.
- Qualified Personnel Requirement – Only authorized Type III Technologies IT personnel, who are trained and qualified for this task, are permitted to generate keys. This prevents unauthorized access and ensures compliance with security standards.
(3) We have transitioned from SSH-1 to SSH-2 due to critical security vulnerabilities and inherent limitations in SSH-1. As SSH-1 is now considered obsolete and insecure, we no longer support its use. To maintain a secure environment, any remaining SSH-1 connections will be immediately upgraded to SSH-2 to mitigate security risks. Moving forward, SSH-2 is the only supported and recommended protocol for secure remote access and encrypted communication.
